Harper Seven AppSec Platform
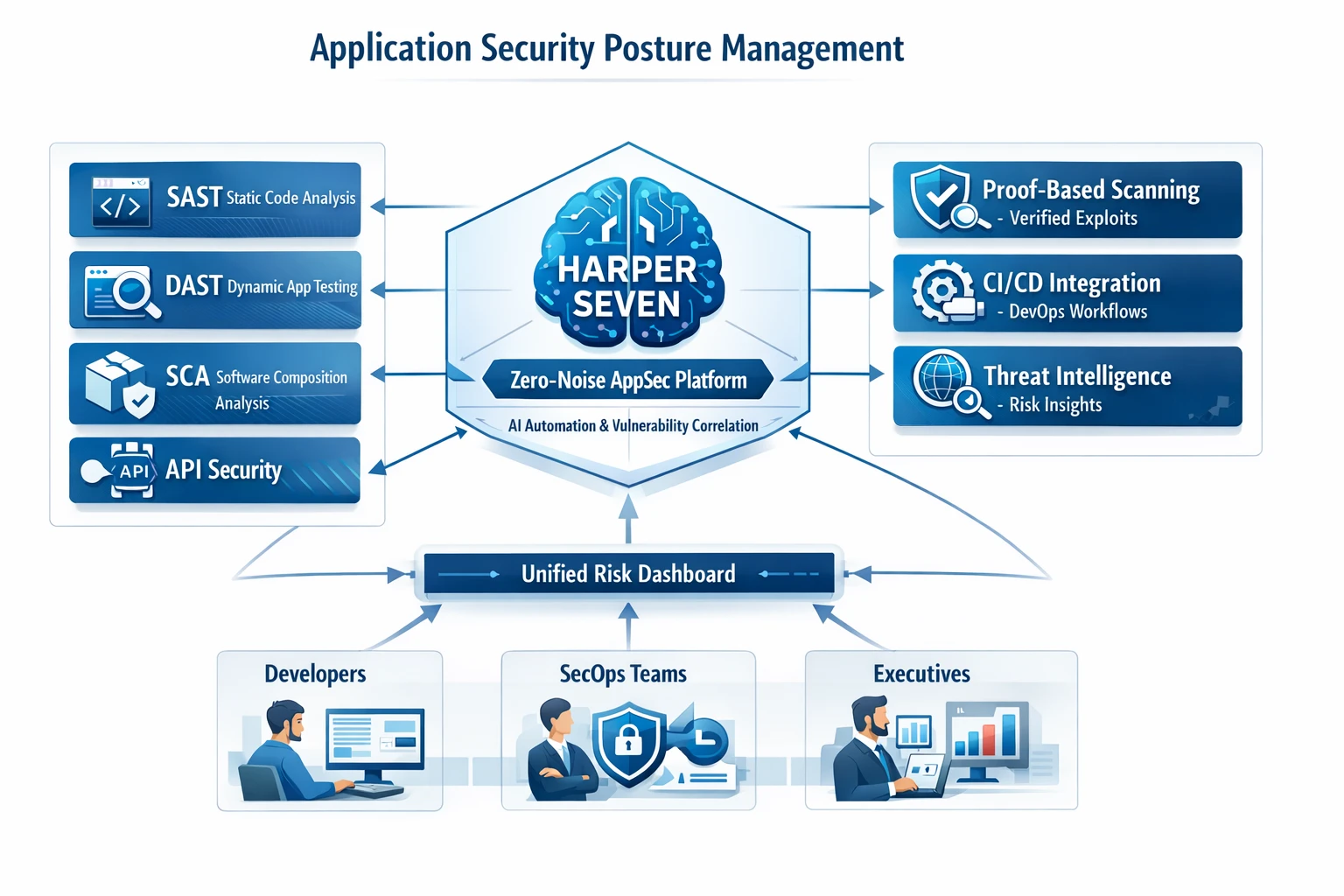
Harper Seven delivers the fastest, most accurate testing tools with AI-powered automation and single-pane vulnerability correlation.
Harper Seven delivers the fastest, most accurate testing tools with AI-powered automation and single-pane vulnerability correlation.
All your AppSec tools in one intelligent platform
ASPM unifies DAST, SAST, SCA, API, container testing, and more under one platform. AppSec leaders see test results in a single view, developers get automated remediation workflows, and organizations track risk with clear KPIs.
Eliminate false positives
Risk across all applications
Continuous across environments
Scale security testing
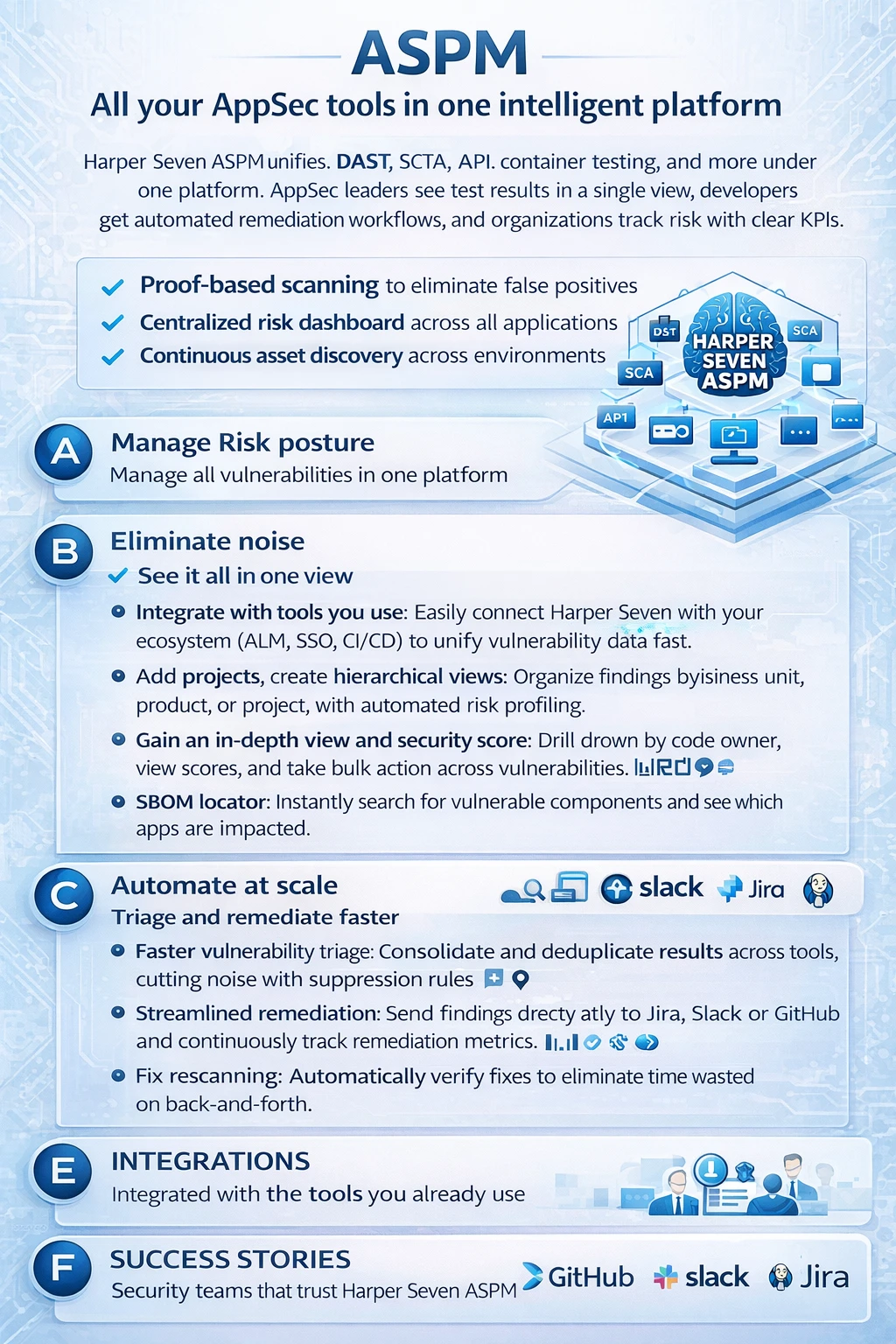
Comprehensive visibility and control over your entire security posture
AI-powered deduplication and false positive elimination
Enterprise-grade automation for continuous security
Developer-friendly workflows and integrations
Seamless integration with your existing tools
Proven results across industries
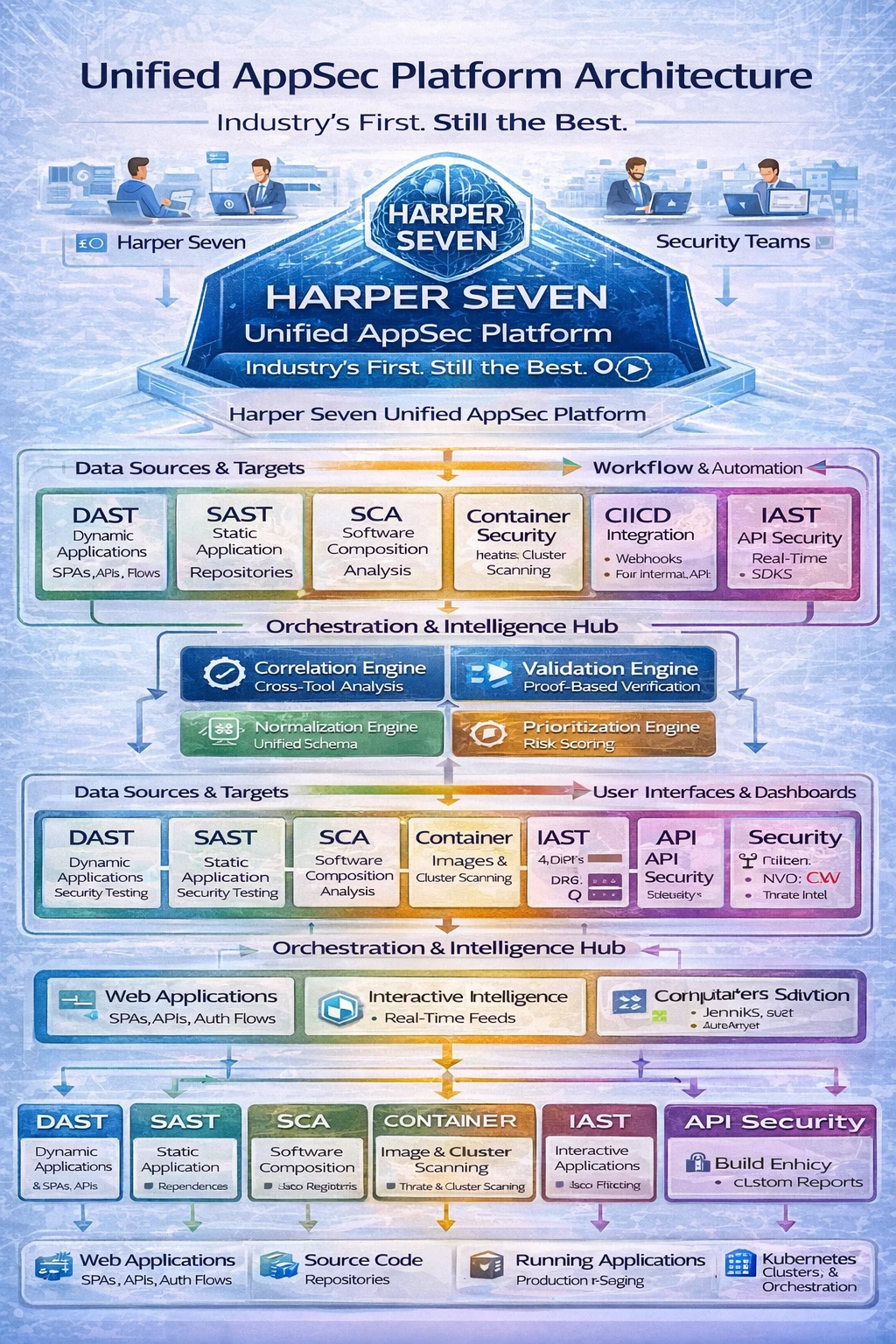
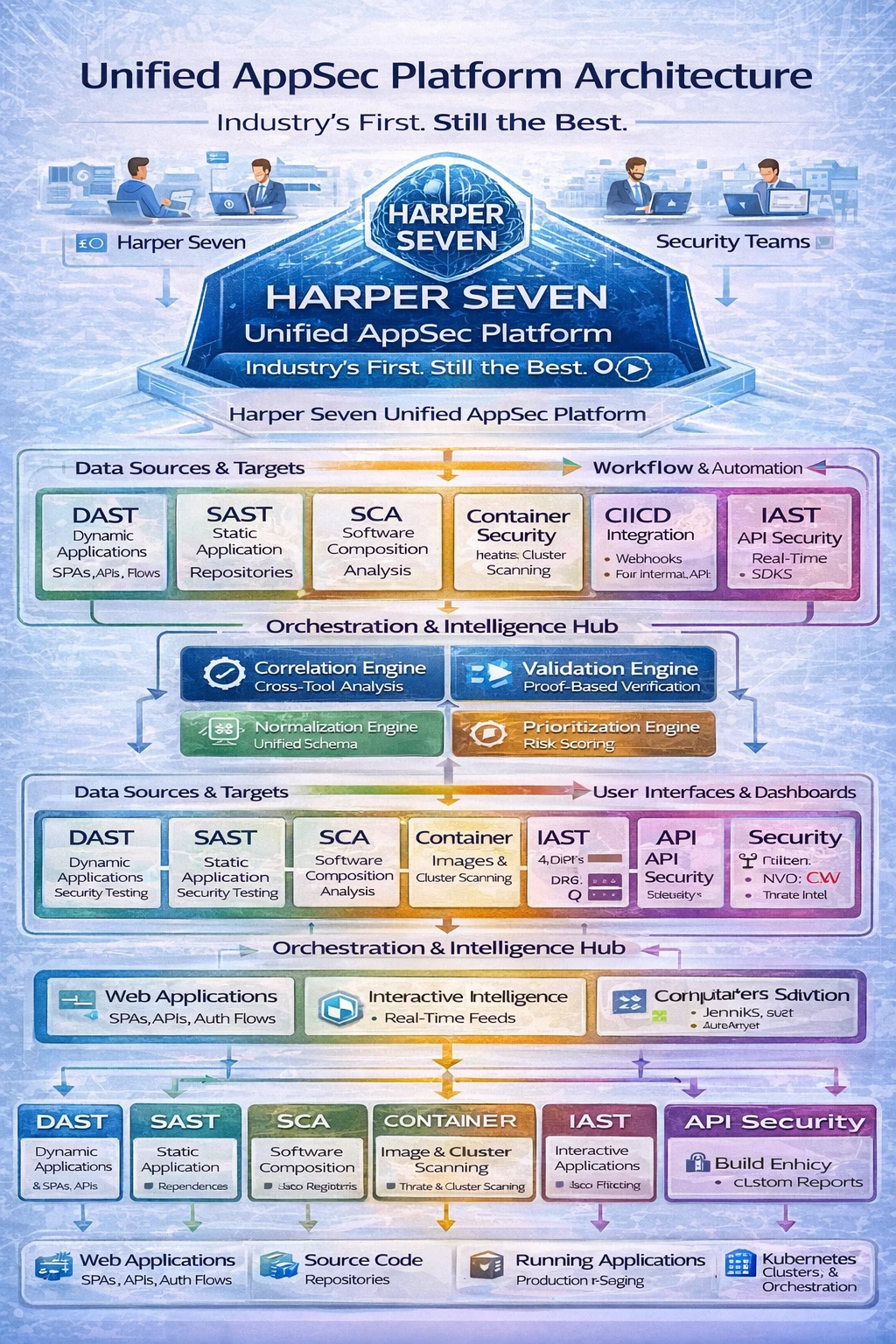
DAST, SAST, SCA, and API findings are normalized into one pipeline.
AI correlation and proof validation remove duplicate and low-confidence results.
Developers, SecOps, and executives view role-based risk outcomes in one place.
Proof-based scanning, CI/CD hooks, and threat context stay fully connected.
Proven exploitability. Zero guesswork.

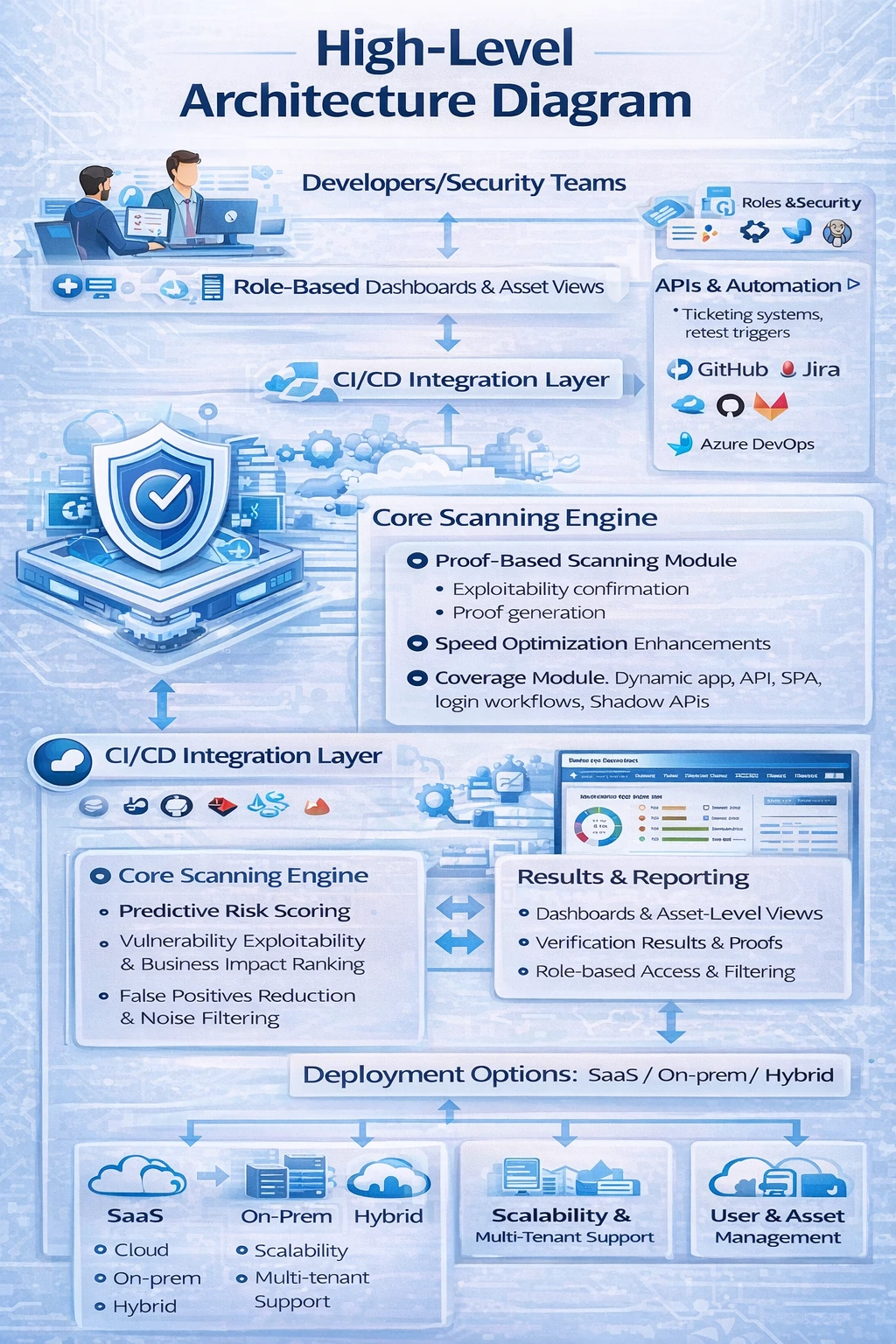
Harper Seven combines industry-leading DAST capabilities with AI-powered automation for the most comprehensive application security testing available.
Every vulnerability comes with exploitability proof, eliminating false positives and providing confidence in results.
Pinpoint exact code locations, AI-powered fix suggestions, and seamless integration with developer workflows.
Shadow API discovery, authenticated scanning, and comprehensive coverage of dynamic applications and SPAs.
Role-based visibility for developers and security teams with live telemetry.
Pipeline hooks trigger scans and synchronize findings into delivery workflows.
Verification-focused scanning confirms exploitability before alerting teams.
SaaS, on-prem, and hybrid models with multi-tenant scalability support.

The industry's first AI-powered unified AST platform
Everything flows through the Orchestration & Correlation Hub with AI Correlation, Deduplication, and Risk Scoring. One vulnerability = one ticket.
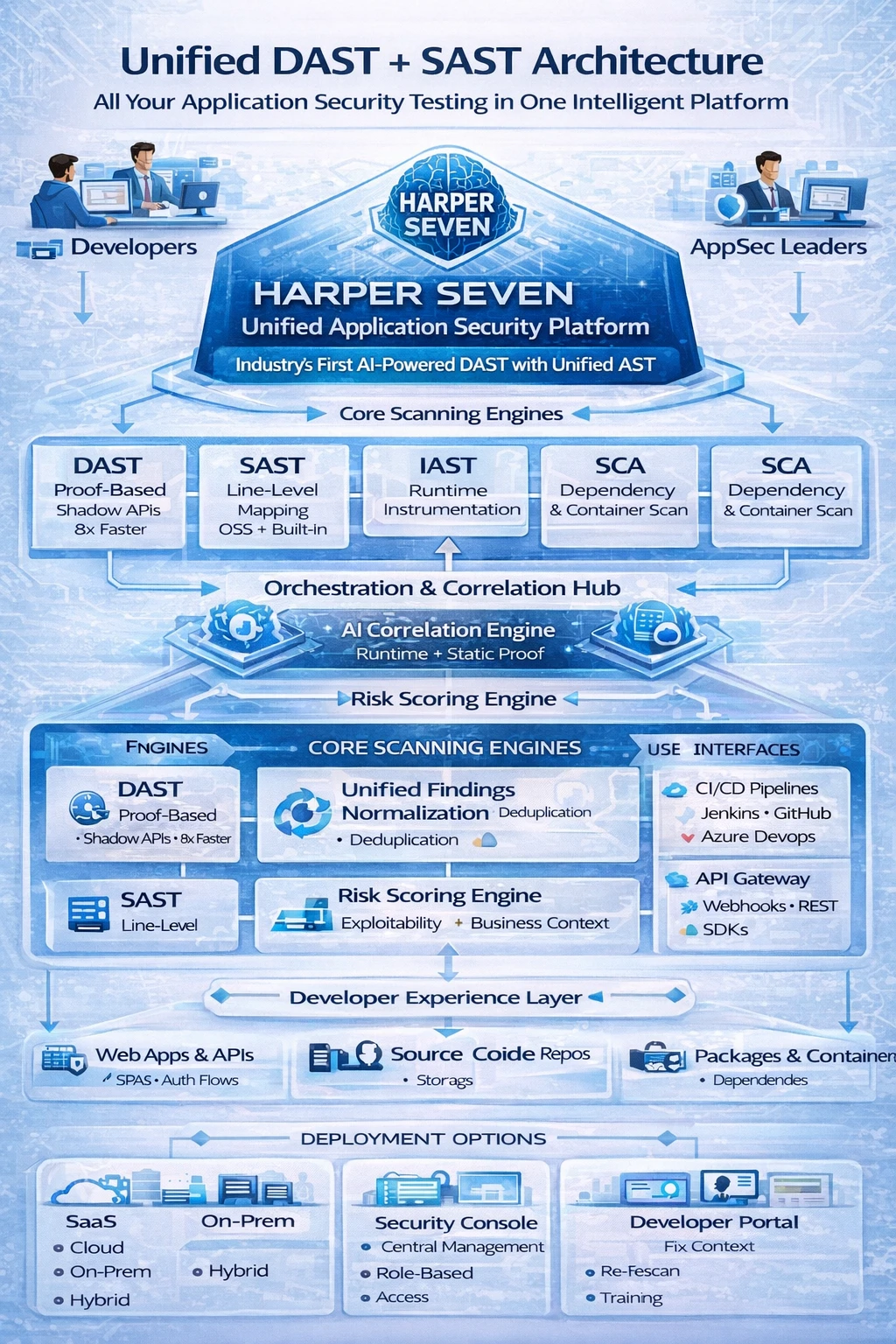

Developers get file + line mapping, suggested fixes, auto-routing, and training feedback loop. Security stops being "thrown over the fence".
Fully managed cloud deployment
Complete control and data sovereignty
Best of both worlds
Take control of open-source risk
Harper Seven brings software composition analysis (SCA) into the same intelligent platform as DAST, SAST, IAST, API Security, and Container Security so you can see and act on component risks with clarity and confidence.
Catch new threats fast
Cut through false positives
No gaps, no delays
All tools in one
Secure every build
Prioritized insights
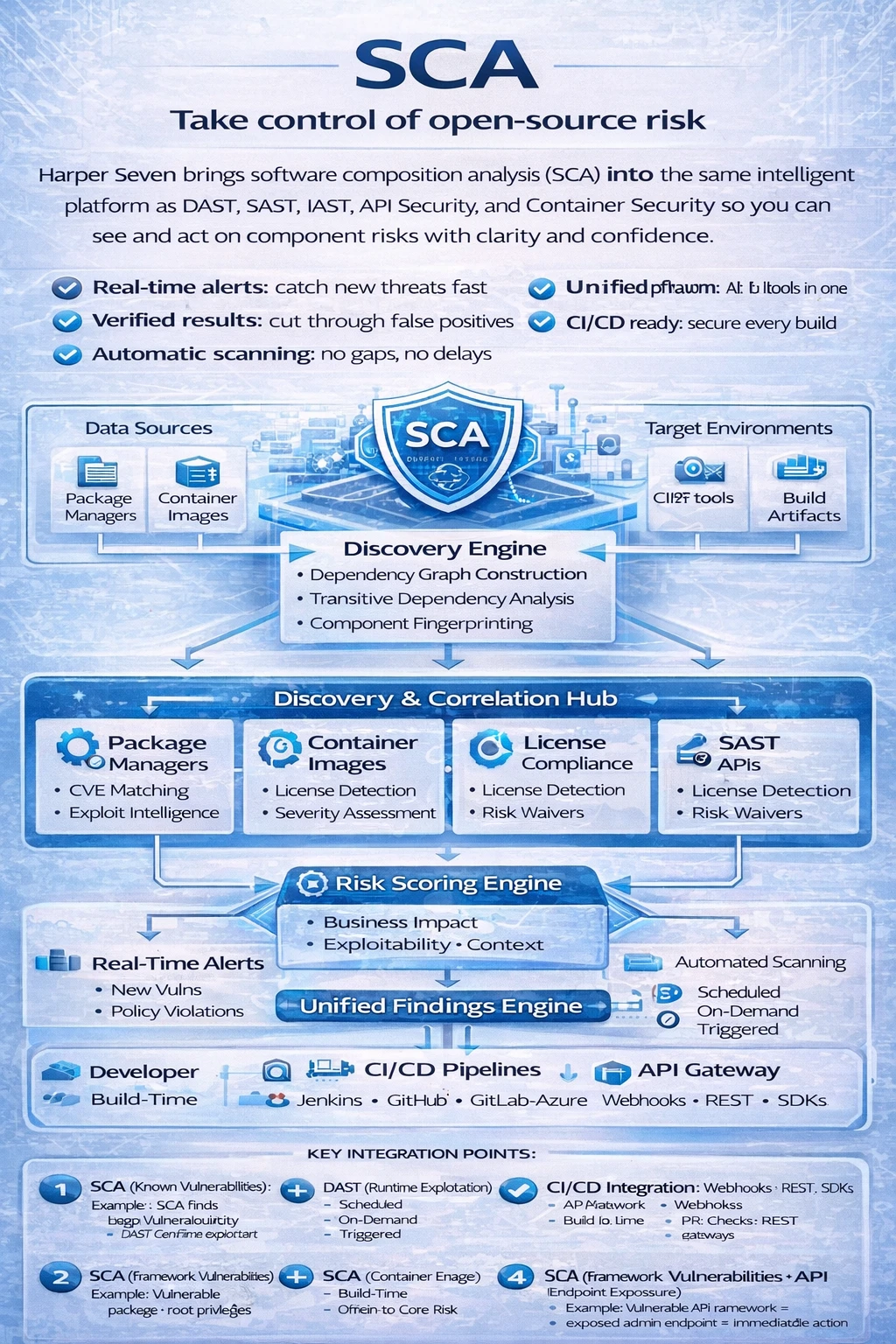
SCA (Known Vulnerabilities) + DAST (Runtime Exploitation) = Confirmed Risk
SCA (Library Risk) + SAST (Custom Code Risk) = Complete Code Risk Picture
SCA (Package Vulnerabilities) + Container (Image Configuration) = Full Container Risk
SCA (Framework Vulnerabilities) + API (Endpoint Exposure) = Contextual Risk
Single dashboard showing SCA + other security findings
Business context + exploitability = actionable items
Direct integration with developer workflows
Automatic discovery across all data sources
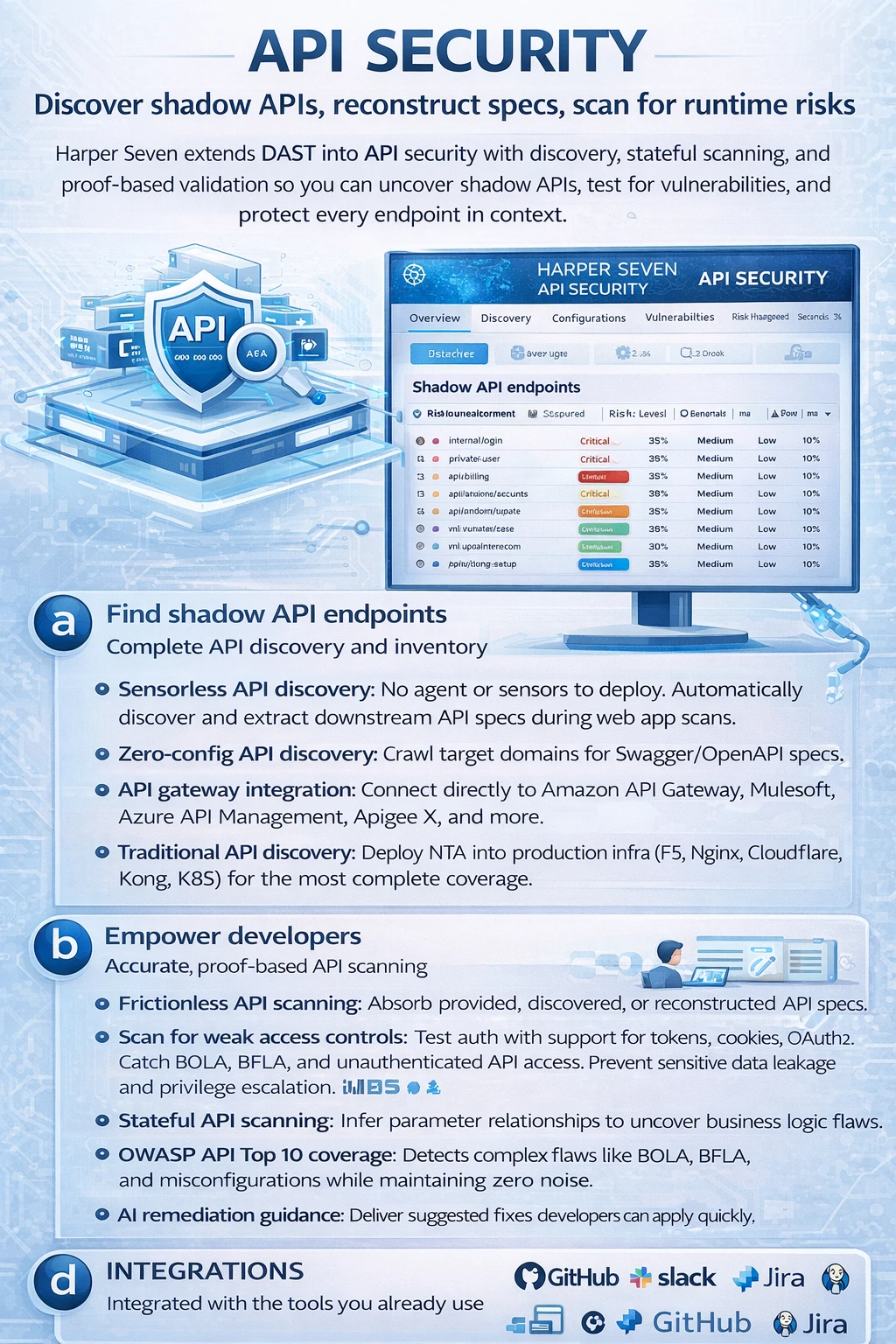
Harper Seven extends DAST into API security with discovery, stateful scanning, and proof-based validation so you can uncover shadow APIs, test for vulnerabilities, and protect every endpoint in context.
Automatically discover undocumented and hidden APIs
Developer-friendly tools and clear remediation guidance
Continuous API testing in CI/CD pipelines
Seamless integration with API gateways and management tools
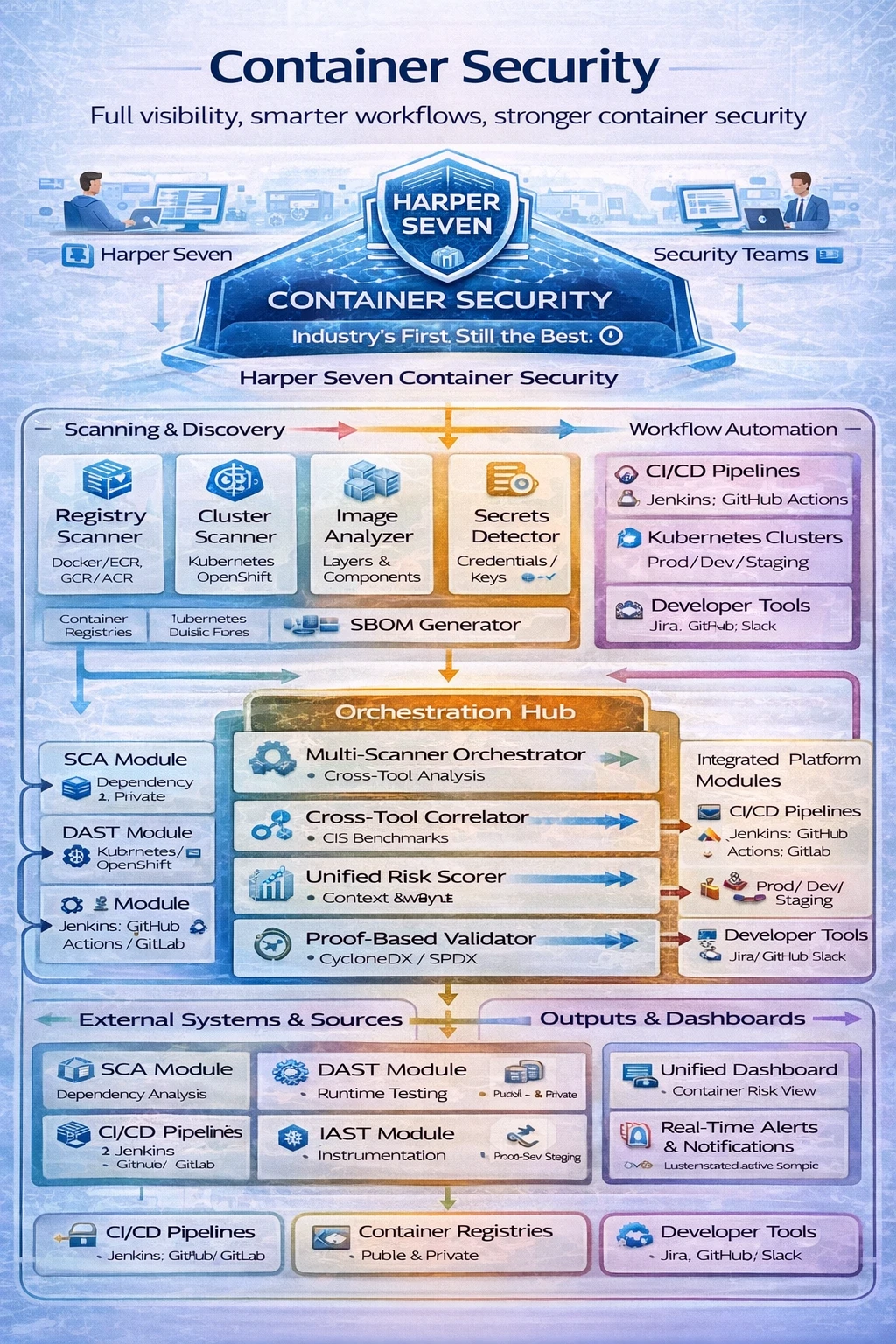
Harper Seven integrates container scanning with SCA, DAST, and CI/CD workflows so you can track vulnerabilities across registries and clusters, cut through complexity, and prioritize container risk in one unified view.
Registries → Scanners → Analysis engines + Clusters & runtime telemetry
Container + SCA + DAST + IAST + API → Unified Risk Score
Validated findings → CI/CD enforcement → Remediation → Developer tools
CI/CD, Registries, Clusters, and Dev tools seamlessly connected
From discovery to deployment - a complete application security lifecycle
Systematically identifies and inventories all digital assets within the organization, including websites, applications, APIs, and concealed or undocumented assets.
Analyzes and evaluates the risk profile of applications and assets, generating risk scores to prioritize security testing and remediation efforts prior to initiating testing procedures.
Conducts comprehensive vulnerability scans across websites, applications, and APIs, achieving a detection accuracy of 99.98% for identified security flaws.
Consolidates and correlates results from multiple security testing tools into a unified dashboard, enabling the prioritization of vulnerabilities based on their assessed risk levels.
Automatically locates hidden or obscured files and configurations that conventional scanners may overlook, pinpointing precise code locations to streamline remediation efforts for developers.
Provides AI-driven remediation guidance, including root cause analysis and step-by-step instructions to effectively address and eliminate vulnerabilities.
Facilitates secure deployment processes by delivering evidence-based validation, AI-guided fixes, and comprehensive compliance reports aligned with standards such as PCI DSS and SOC 2.
Schedule a personalized demo to see how our unified AppSec platform can transform your security posture.